Summary
A Critical Broken Authentication vulnerability exists in Known 1.6.2. The application leaks the password reset token within a hidden HTML input field on the password reset page. This allows any unauthenticated attacker to retrieve the reset token for any user by simply querying the user's email, leading to full Account Takeover (ATO) without requiring access to the victim's email inbox.
Details
The vulnerability occurs within the password reset flow. When a reset is requested, the application generates a verification code. However, the subsequent reset page (/account/password/reset/) incorrectly reflects this code back to the client in the HTML source code.
Specifically, the sensitive token is embedded in:
Because this page is accessible via a GET request using the victim's email as a parameter, an attacker can programmatically extract the token.
PoC
- The attacker asks for a password reset for the victim


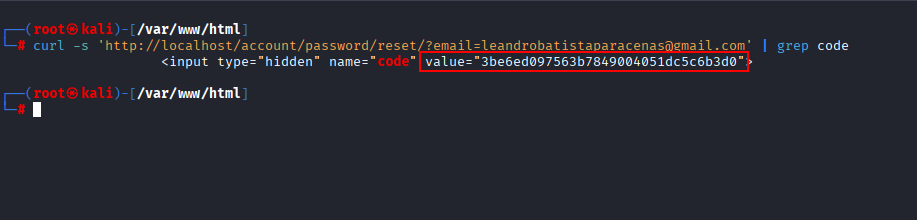
- The attacker makes the following curl command on the terminal using the victim's email, and is able to get the code that was sent as an hidden field in the HTML.
- With this code, the attacker is able to use it in order to reset the victim password.


- The attacker is able to login with the new password.


Impact
- An attacker can compromise any account on the platform, including administrative accounts, resulting in total loss of Confidentiality, Integrity, and Availability.
References
Summary
A Critical Broken Authentication vulnerability exists in Known 1.6.2. The application leaks the password reset token within a hidden HTML input field on the password reset page. This allows any unauthenticated attacker to retrieve the reset token for any user by simply querying the user's email, leading to full Account Takeover (ATO) without requiring access to the victim's email inbox.
Details
The vulnerability occurs within the password reset flow. When a reset is requested, the application generates a verification code. However, the subsequent reset page (/account/password/reset/) incorrectly reflects this code back to the client in the HTML source code.
Specifically, the sensitive token is embedded in:
Because this page is accessible via a GET request using the victim's email as a parameter, an attacker can programmatically extract the token.
PoC
Impact
References